TEE.fail Got the Headlines Right and the Conclusions Wrong
The TEE.fail Research: Why It Makes Me More Bullish on TEEs, Not Less
This article is derived from a Twitter thread by Rahul Saxena (@saxenism). Source: x.com/saxenism/status/1986405126010200366
The TEE.fail research broke the confidentiality and integrity guarantees of TEEs, and that's huge. But the way it's being presented feels more like a hit-piece than an honest discussion. Let's unpack what this attack actually requires, what it actually demonstrated, and why, when you look at it clearly, it makes a strong case for TEEs and not against them.
The Attack Requires Far More Than "Physical Access"
The TEE.fail team's work is impressive. But the framing that "whoever has physical access can exfiltrate data, assets, and even break verifiability" is not accurate.
For this attack to work, the attacker needs both physical access and software root access simultaneously. The paper is explicit about this:
"We assume an attacker with physical and root-level access to the target machine. For physical access, we assume adversarial capabilities of an electronics hobbyist, capable of simple electrical assembly operations (i.e., soldering) as well as installing components into the target machine. However, we note that our attacks do not require more advanced capabilities such as PCB circuit editing, or chip-level inspections using electron microscopes. For software access, we assume a root-level adversary, capable of performing arbitrary configurations to the target. This includes modifying settings, installing a custom kernel and drivers, as well as adversarially manipulating the target's userspace setup and memory mappings."
What does root actually mean here? Physical root means the attacker can do whatever they want with the hardware: plug and unplug DIMMs, add interposers, attach probes, access an on-site serial console, force reboots, and make BIOS changes. Software root means the ability to flush caches, pin virtual pages to specific physical frames, manipulate page tables, and load or unload kernel modules.
These are just the prerequisites. On top of that, the attacker must physically place an interposer between the DIMM and DIMM slot, lower the memory bus rate to 3200 MT/s (well below the JEDEC baseline for DDR5 at 4800 MT/s), and have concurrent software access to force cache flushes, page pinning, and more. This is the setup. The actual attack comes after.
Not All TEEs Were Compromised Equally
The claim that the research "affects not just Intel TDX but also AMD SEV-SNP and Nvidia's GPU Confidential Computing" is technically true, but the sweeping presentation implies identical compromise across all three, which is not the case.
For Intel SGX and TDX, researchers were able to extract platform attestation keys (PCKs). For AMD SEV-SNP with ciphertext hiding enabled, researchers extracted OpenSSL ECDSA signing keys. These are application-level keys, not AMD's attestation or platform keys. For Nvidia's GPU Confidential Computing, a forged TDX attestation is a pre-requisite for the attack. What the paper demonstrates is an attestation relay attack, not a direct GPU compromise.
Nobody is dismissing the severity of extracting Intel TDX and SGX attestation keys; that is genuinely damning. But grouping all three TEE vendors into one sweep without distinguishing what was actually extracted from each misdirects the conversation.
What Happens After PCK Extraction?
Once the platform attestation keys are extracted, the consequences are real and severe. Secure block building, privacy-preserving AI training and inference, TEE-based DEX front-running protections: all of these collapse. If you extract the attestation keys of a TEE, it has been stripped of all its power. Post-acquisition, an attacker can forge attestations, impersonate the TEE to any verifier, and ultimately exploit any application or protocol that trusted the TEE's integrity guarantees.
This is not in dispute. What is in dispute is how difficult it actually is to reach that point in a real-world production environment.
What This Attack Actually Costs in the Real World
The claim that "anyone can perform this attack with cheap, hobbyist level equipment for under $1000" is where the framing breaks down most severely.
The $1000 figure refers to the cost of the physical equipment used in the lab. It does not account for what an attacker would actually need to do to execute this against a production TEE deployment inside a major cloud provider's data centre.
A Tier 3+ data centre means armed guards, tamper-proof locks, on-site security operations centres, camera surveillance, airgapped entry gates, and thorough supply-chain integrity checks on hardware. Getting to a specific server requires either compromising a high-ranking insider with both physical and software-level access, or obtaining that position yourself.
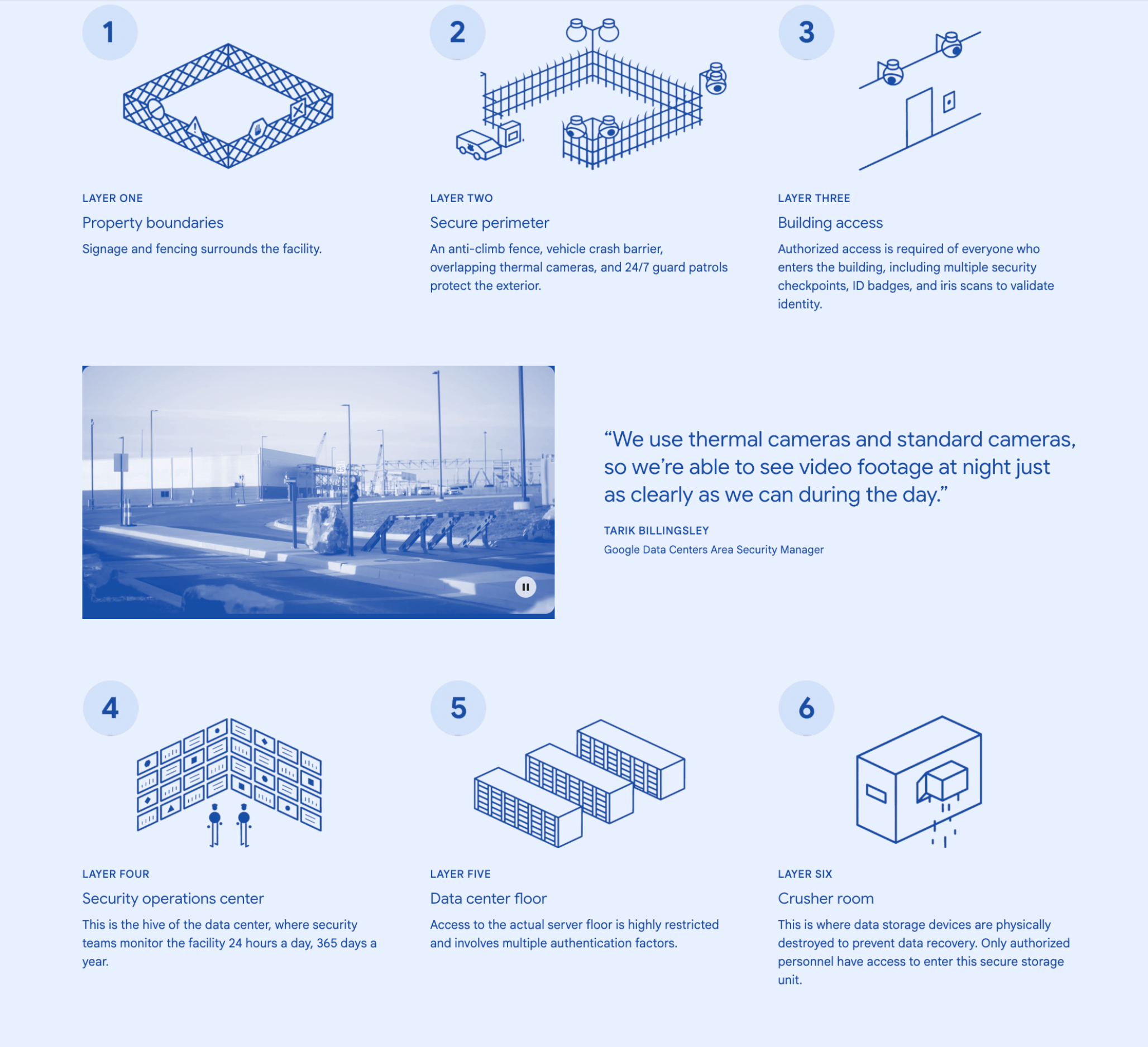
Once inside, the attacker needs to conduct reconnaissance, procure and conceal equipment, and execute the attack under strict operational time constraints. A Tier 4 data centre allows only 26.3 minutes of downtime per year.
The attack also requires BIOS and firmware changes to lower the memory bus speed. In any hyperscaler environment, this immediately triggers performance monitoring and image integrity checks, causing the affected server to be pulled from production rotation. And even if everything proceeds without detection, a single reboot (which the paper explicitly requires) triggers live migration of all workloads to a clean instance.
In most cloud TEE deployments, cloud tenants have neither hardware nor software root access. Data centre staff may have physical access but not isolated software root on target VMs. This dual-requirement eliminates the vast majority of potential attacker profiles.

Now consider a protocol using m-of-n TEE threshold signing with geographically distributed enclaves across independent cloud providers. Executing this attack against a single TEE is already highly resource-intensive. Executing it across enough TEEs to break a threshold scheme multiplies the cost exponentially. This is well beyond any hobbyist's reach and approaches nation-state territory.
Central Points of Failure Are Not New
A common reaction to this research is: TEEs are a central point of failure and therefore shouldn't be used. But the entire web3 industry runs on central points of failure. Protocols rely on oracles. Entire L2s run with a single sequencer. The industry collectively runs on Github, npm, Docker, Notion, Telegram, and Gmail: infrastructure that developers have essentially no control over.
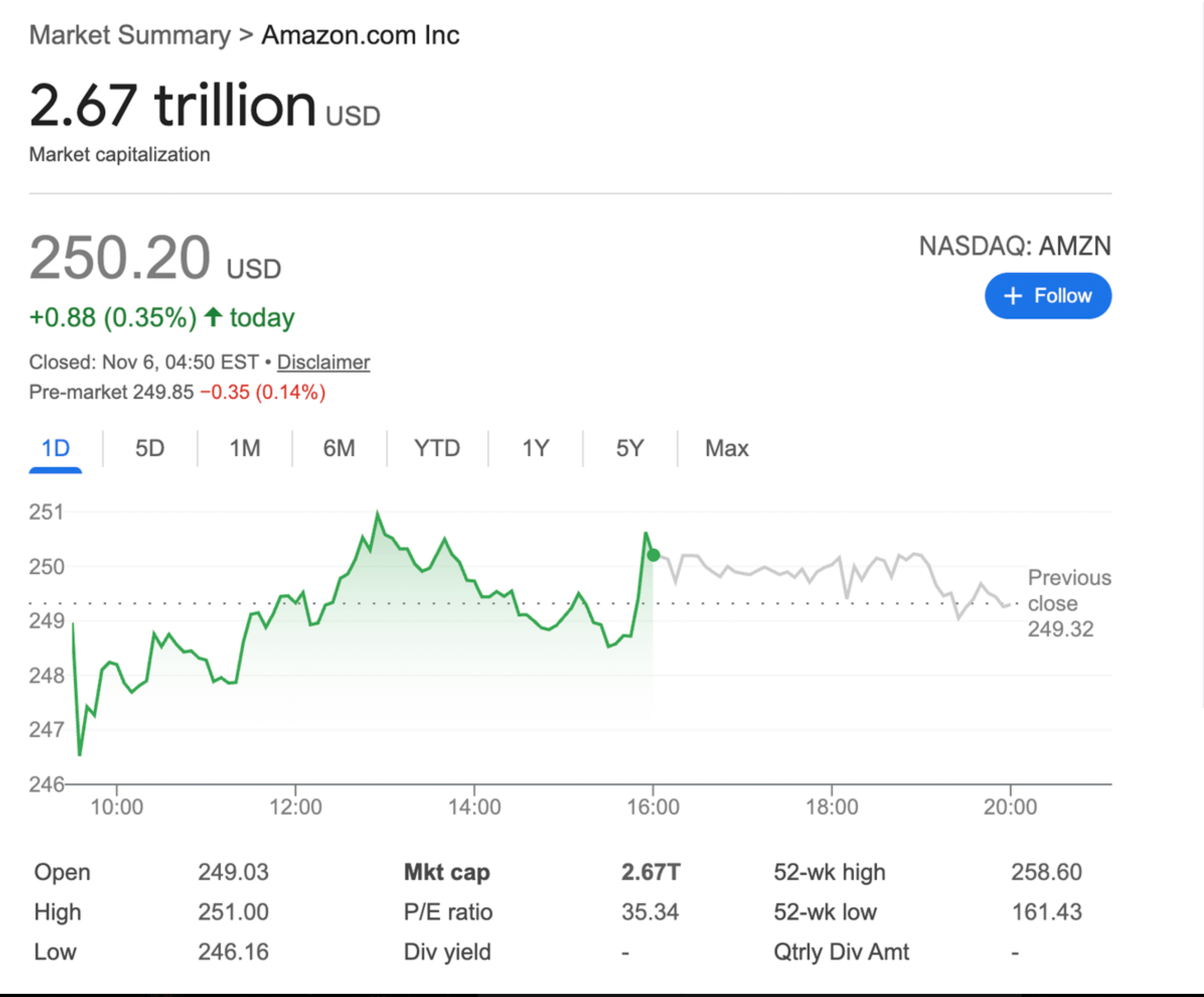
If a Cloud TEE solution is good enough for a bank, which has infinitely more regulatory overhead and legal threats than a DeFi protocol, it is good enough for your use case too. Amazon is a company with a market cap well north of $2.5 trillion. They are not going to compromise your DeFi protocol.
A centralised point of failure is not something that should be categorically avoided. It's something that should be understood, threat-modelled properly, and mitigated through protocol design. TEEs are no different.
To safely use TEEs, protocols need to upgrade their threat models, design for resilience rather than assuming the TEE is infallible, and write enclave-grade code: constant-time cryptography, avoidance of predictable access patterns, and architecture that degrades gracefully rather than failing catastrophically. An m-of-n TEE threshold signing scheme across geographically distributed providers is a concrete example of this kind of resilient design.
Why This Research Actually Makes TEEs More Credible
The strongest argument for TEEs is not that they are unbreakable. It's that they are mature enough to attract serious adversarial research.
TEEs have been running in payment terminals, smartphones, and cloud infrastructure for years, battle-hardened in environments with real stakes far outside the web3 ecosystem. The fact that top academic research groups are dedicating significant resources to breaking them is a signal of maturity, not fragility. Scrutiny produces hardening.
Contrast this with ZK, FHE, and MPC. These are powerful and promising technologies, but they have far fewer production deployments and consequently far fewer researchers actively trying to break them. Less public scrutiny means less hardening. From a security-maturity standpoint, a well-audited TEE deployment today is a more defensible choice than a novel cryptographic stack that only a small number of experts genuinely understand end-to-end.
The TEE.fail paper forced the industry to confront real attack vectors, sharpen its threat models, and build more resilient protocols. That is exactly what good security research is supposed to do.
The goal is not to choose TEEs over ZK or FHE or MPC. It's to combine all of these stacks thoughtfully, with TEE security understood clearly enough to use it as a component in a broader system that no single failure mode can bring down.
This article is derived from a Twitter thread by Rahul Saxena (@saxenism). Source: x.com/saxenism/status/1986405126010200366
